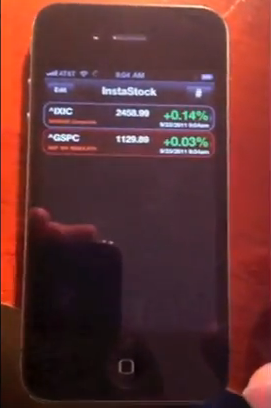
A developer has managed to get an app approved for the iPhone that allows malicious code to be run after it is installed. The app appears to just provide stock information, but in the backgroud it actually opens up an exploit which can then allow code to be injected in. Tasks like grabbing an address book can be done remotely after the app is installed.
The app has now been pulled and the developer banned from the developer program although the developer, Charlie Millier, appears to have no bad intentions and was merely highlighting the problem so Apple could patch it up.
The termination came just hours after Miller made the loophole public, and according to Apple is “effective immediately.” The company’s justification is the fact that the exploit was hidden inside a stock ticker app shell, and contravenes the section of the App Store agreement that forbids a developer from using such a system to “hide, misrepresent or obscure” software.
Charlie Miller is a security researcher who has reported a number of other bugs in the past. This particular problem/bug was opened due to Apple attempting to speed up JavaScript performance on the browser. In doing so, it opened a problem up which can be exploited by users.
Expect a patch to be available soon although we are unsure if Charlie will get his account back.
The video below gives a full demonstration of the app (which is now pulled) and how it was used to grab data from the iPhone.





Speak Your Mind
You must be logged in to post a comment.